Strengthening Network Traffic Security in Modern IT Infrastructure
As organizations expand their digital operations, the volume of data flowing across networks continues to increase. The businesses are dependent on integrated systems, cloud environments, and web applications to provide services to consumers worldwide. Although this connectivity aids innovation and efficiency, it exposes them to cyber threats. Network traffic security has therefore, emerged as a serious concern for those organizations that seek to keep confidential information and provide stable digital services.
Network traffic security involves monitoring, controlling, and protecting data as it flows between users, applications, and infrastructure systems. Through proper security measures, companies can avoid unauthorized access, identify suspicious activities, and have a secure communication channel in their systems.
Growing Importance of Traffic Security
The contemporary IT environment is much more complicated than conventional networks. Most of the organizations have hybrid systems, which are cloud systems in combination with remote devices and on-premises infrastructure. The communication between these components is continuous, with applications exchanging data and users engaging with digital services.
This is due to the continuous flow of data, which presents several points of vulnerability to possible cyber-attacks. Hackers can focus on interception of communication, malicious code injection, or flooding systems. Unless security measures are employed adequately, such attacks may cause service interruption, data breaches, and losses.
Monitoring and Visibility Across Network Traffic
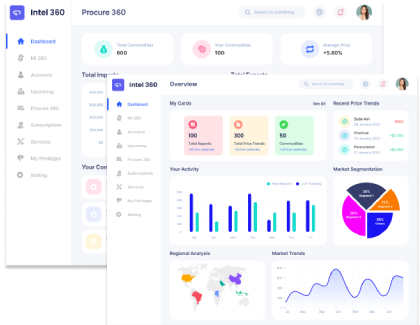
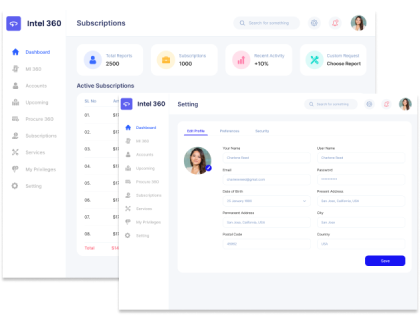
Effective network security begins with establishing strong visibility into data flow across the infrastructure. Monitoring tools enable IT teams to track the traffic flows and system performance and identify abnormal patterns, which can be a sign of a threat.
Advanced monitoring systems have the ability to collect data from various devices such as routers, servers, and applications. This enables them to offer a wide view of all activities taking place within the network. This, in turn, enables them to understand how their systems interact with one another, thus helping them to identify any possible weaknesses. In case of any unusual activities, such as increased traffic or unauthorized connection attempts, security teams can act swiftly.
Incidents are also well-responded with the aid of continuous monitoring. Analysis of real-time traffic data will allow organizations to isolate the affected systems and impose protective measures before the threat spreads throughout the network.
Encryption and Secure Communication Channels
Encryption is a critical aspect of network traffic security. Information transmitted over the internet may pass through multiple networks before reaching its intended recipient. In the absence of encryption, it may intercept confidential information, including login credentials or any other sensitive messages.
Encryption technology is used to encrypt data that can be read and understood by the authorized systems only. Secure communication protocols are used to give the sender and the receiver a chance to identify each other before transacting information. This helps avoid unauthorized access and defend the integrity of the information that is carried over.
Organizations are increasingly using encrypted connections in their internal and customer-facing systems. By securing communication channels across every segment of the network, businesses can minimize the risk of data exposure and build trust with users.
Protecting Infrastructure from Traffic Based Attacks
A DDoS attack is one of the most prevalent attacks on the stability of the network. During this kind of attack, attackers overload a system or network with heavy volumes of traffic, thus crippling servers and blocking access to services by legitimate users.
Traffic security solutions can be used to counter such attacks by analyzing patterns of requests and blocking out suspicious traffic. Automated systems can detect abnormal traffic and redirect or block it, preventing harmful requests from affecting infrastructure performance.
The other protection strategy is network segmentation. Organizations subdivide infrastructure to reduce the dispersion of possible attacks. In case one section of the network gets compromised, then the rest of the parts will be isolated and secure. The strategies guarantee that services do not go offline even when a disruption is attempted, allowing organizations to carry on with their operations.
Explore network traffic management technologies in the Load Balancer Market Report.
Creating Secure and Reliable Digital Networks
Data security of network traffic has become necessary to ensure reliable and consistent digital services. With businesses progressively increasing their online presence, tough security measures are emerging as a basic aspect of infrastructure planning. Surveillance systems, encryption protocols, and automatic threat detection systems are all part of the safer environment of the network.
Within the framework of an investment in extensive traffic security measures, it is possible to minimize the risks, protect confidential data, and ensure the non-stop functioning of applications. A safe network does not just help to secure infrastructure but also helps to promote long-term growth by making sure that customers and partners can communicate with the digital services without any fear.
















Share